
Microsoft Security Essentials Download
free
Download
Review Microsoft Security Essentials
Microsoft Security Essentials is an anti-virus, anti-spyware, and anti-malware developed by Microsoft that is free for home users and small businesses.
Having basic protection in the Windows operating system is essential to be able to make use of a PC. If we don't have an antivirus or antispyware, in a very short time, our PC will be affected by some malware or virus on the Internet.


Microsoft Security Essentials is presented as an effective solution to viruses, trojans, adware, spyware, and other malware. If we have installed the operating system, and your PC doesn't have an anti-virus, this software will be perfect for us because it's free and offers basic protection for Windows XP, Windows Vista, and Windows 7. It can be used free for home users and small businesses (up to 10 computers).
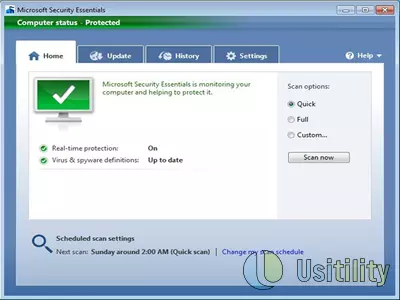
Software installation is quick and easy. Once installed, we will see a small icon on the right side of the taskbar. This icon indicates the computer protection status; if it is green, it means that the PC is protected against threats.
To open the program, we can double-click on the icon in the taskbar. Once opened, it displays a screen where we can see a summary of the protection status. It will show the last virus scan and when the next scan is scheduled. We can also run a scan: quick, full, or custom.
The release of new viruses and variants of old ones makes it necessary to have an antivirus with the latest virus information and also can be upgraded easily. In this case, this antivirus program automatically updates viruses, malware, and other threats database without our intervention. So we always will have fresh protection against viruses. At any time, we can click on the “Update” button to force the program to download the latest virus and spyware definitions.
If the anti-virus detects malicious software, it warns us and assigns a level of alert to the detected threat. Alert levels are:
- Maximum: potentially dangerous threat. The anti-virus will attempt to eliminate the threat without prompting the user.
- High: a threat that can affect users' privacy and damage the system. Anti-virus will attempt to delete the threat without consulting the user.
- Medium: the threat that can harm the computer and user's privacy. The antivirus asks what we want to do with that threat.
- Low: the threat that can collect information about the computer and make changes. The antivirus will ask us what action we want against the threat.
When the anti-virus detects a threat, it shows us several things we can do:
- Delete: the anti-virus will attempt to delete the detected threat, deleting all the infected files.
- Quarantine: this option allows us to disable the file containing the threat. To do this, the antivirus moves the infected file and will be located where it can't run automatically. Once we decide what to do with that file, we can remove it from the quarantine to either delete it or guarantee access to our system.
- Enable: if we trust the file triggering the alert, we can allow it to run. We should use this option with caution because we risk giving access to malicious files.
We can see the history of threats found, deleted, quarantined, and allowed at any time. In this way, we can see when was the first time that a virus was detected or when a certain threat was removed.
Even though Microsoft Security Essentials is a basic antivirus, it has advanced options that will be enough for many users. Some of these options are:
- Schedule scan: we can choose the day of the week and the time when the scan starts. We can limit CPU usage while auto scan, avoid overloading the PC, and slow down the rest of ongoing operations.
- Real-time protection: this option allows the antivirus to scan all those programs and files that try to be installed or saved on the computer. This way, we'll solve the problem before it happens since the antivirus will detect the threat and act accordingly to the danger associated with such a threat.
- Examine compressed files: this option enables the analysis of the files inside .zip, .rar, .cab, etc.
- Create a restore point: if we mark this option, it will create a restore point just before we delete or quarantine detected threats.
- Delete quarantine files: this option allows us to define the expiration time for files in the quarantine folder. We can choose between 1 day and 3 months. If, for example, we chose 3 months, all those files that have been in quarantine for 3 months will be deleted from the computer. This way, we avoid the store unusable and infected files in our system.
There are the most powerful antivirus than this one, but if we still don't know which antivirus to purchase, this will be a perfect solution to be installed when we decide to go for a complete antivirus program.
Frequently Asked Questions
- Is Microsoft Security Essentials downloadable for Windows 7?
- Yes, this software can be downloaded and is compatible with Windows 7.
- What operating systems is it compatible with?
- This software is compatible with the following 32-bit Windows operating systems:
Windows 7, Windows Vista, Windows XP.
Here you can download the 32-bit version of Microsoft Security Essentials.
As for Windows 64-bit, this software is compatible with:
Windows XP 64-bit, Windows Vista 64-bit, Windows 7 64-bit.
Here you can download the 64-bit version of Microsoft Security Essentials. - Is it compatible with 64-bit operating systems?
- Yes, it is compatible with Windows 64-bit, in the following link you can download the 64-bit version.
- What files do I need to download to install this software on my Windows PC?
- To install Microsoft Security Essentials on your PC, you have to download the MSEInstall.exe file to your Windows and install it.
If you want to install the 64-bit version, you will need to download the MSEInstall.exe file and install it on your Windows. - Which version of the program am I going to download?
- The current version we offer is the 4.10.0209.0. For Windows 64-bit the version we offer is the 4.10.0209.0.
- Is Microsoft Security Essentials free?
- Yes, this program is free so you will be able to use it without any limitations, and without additional cost.
- Home
- Microsoft Security Essentials home
- Category
- Operating Systems
- Windows 7
- Windows Vista
- Windows XP
- Windows XP 64-bit
- Windows Vista 64-bit
- Windows 7 64-bit
- License
- Freeware